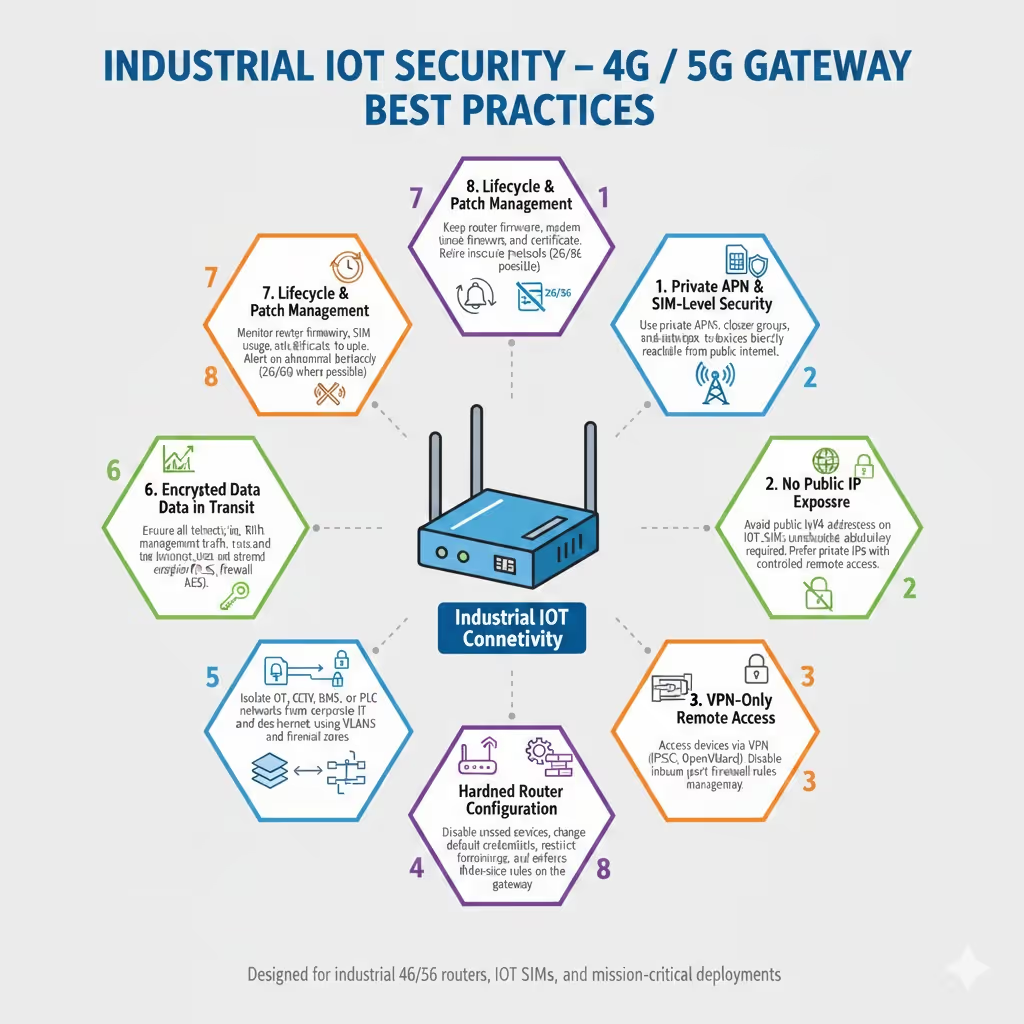
Industrial IoT Security Best Practices
4G / 5G Gateways, Routers and IoT SIM Connectivity
Industrial IoT security is often misunderstood.
Most security advice online focuses on passwords, cloud APIs, or consumer IoT devices. In real-world industrial deployments using 4G and 5G gateways, the biggest risks sit at the network layer, not the application layer.
This guide explains how IoT security actually works when deploying industrial cellular routers, IoT SIM cards, and remote assets such as CCTV, BMS, EV chargers, energy systems, kiosks, and control equipment.
The Core Principle: Don’t Expose Devices to the Internet
The single biggest IoT security mistake is this:
Giving a device a public IP address and exposing services directly to the internet.
Once a device is publicly reachable, everything else becomes damage control.
Industrial IoT security works best when devices are:
- Not publicly addressable
- Accessible only via controlled tunnels
- Isolated from the wider internet by design
1. Use Private APNs and SIM-Level Security
IoT SIM cards are not the same as consumer mobile SIMs.
A properly designed IoT SIM should use:
- Private APN connectivity
- Closed user groups
- Network-level isolation between customers
- Controlled routing to backend systems
This means devices:
- Are not reachable from the public internet
- Can only communicate with approved destinations
- Are protected before traffic ever reaches the router firewall
SIM security is your first line of defence, not an afterthought.
2. Avoid Public IP SIMs Wherever Possible
Public IP SIMs are widely sold, but widely misunderstood.
They are sometimes necessary, but in most deployments they:
- Increase attack surface
- Require constant firewall hardening
- Expose management interfaces if misconfigured
- Create long-term security and compliance risk
In most cases, a private IP SIM plus VPN access is a more secure and scalable approach.
If a public IP is used, it must be:
- Locked down with strict firewall rules
- Never combined with open port forwarding
- Monitored continuously
3. Use VPN-Only Remote Access
Remote access should always be outbound from the device, never inbound from the internet.
Best practice is:
- VPN initiated from the router to a secure server
- No WAN-side management access
- No exposed web interfaces
- No open inbound ports
Common VPN technologies used in industrial deployments include:
- IPSec
- OpenVPN
- WireGuard
The key principle is simple:
If the VPN is down, the device is unreachable.
That is exactly what you want.
4. Harden the Gateway Configuration
Industrial routers ship with many features enabled to support different use cases. Not all of them should be active.
Minimum hardening steps:
- Change default usernames and passwords
- Disable WAN-side management access
- Disable unused services and protocols
- Restrict management access to LAN or VPN only
- Apply strict firewall policies
Routers should be treated like infrastructure equipment, not consumer devices.
5. Segment Networks and Devices
Never place everything on a single flat network.
Typical segmentation includes:
- LAN vs WAN separation
- OT devices isolated from IT systems
- CCTV isolated from corporate networks
- Management traffic separated from data traffic
VLANs and firewall zones allow:
- Reduced lateral movement if a device is compromised
- Safer multi-device deployments
- Easier compliance with security standards
6. Encrypt All Data in Transit
Encryption is non-negotiable.
Ensure:
- VPN tunnels use modern encryption
- Telemetry is sent over TLS
- Management traffic is encrypted
- Legacy unencrypted protocols are avoided
Encryption protects:
- Data confidentiality
- Credentials
- Control traffic
- Integrity of commands sent to devices
7. Monitor Connectivity and Behaviour
Security is not just prevention. It is visibility.
Monitoring should include:
- SIM data usage patterns
- VPN connection status
- Device uptime and connectivity
- Unexpected traffic behaviour
- Repeated reconnection or authentication failures
Abnormal behaviour often signals:
- Misconfiguration
- Failing hardware
- Network issues
- Security incidents
8. Manage Firmware and Device Lifecycles
Unpatched devices are vulnerable devices.
Best practice includes:
- Keeping router firmware up to date
- Updating cellular modem firmware when required
- Removing legacy protocols
- Planning for 2G/3G sunset impacts
- Replacing unsupported hardware
Security is an ongoing process, not a one-time setup.
What Actually Keeps Industrial IoT Secure
To be clear, real-world industrial IoT security is built on:
- Network isolation
- Private SIM connectivity
- VPN-based access
- Strong firewall policies
- Controlled remote management
- Continuous monitoring
Passwords and MFA help, but they are secondary controls, not the foundation.
How Millbeck Approaches IoT Security
At Millbeck, we design IoT connectivity around:
- Private and roaming IoT SIM solutions
- Secure VPN-based remote access
- Industrial-grade 4G and 5G gateways
- Practical, deployable security architectures
Security is built into the connectivity design, not bolted on afterwards.
If you are unsure whether your current deployment follows these principles, we are happy to review it.
Need Help Securing a Deployment?
If you are deploying or managing:
- Industrial 4G or 5G routers
- CCTV or BMS over cellular
- EV charging infrastructure
- Remote monitoring or control systems
Millbeck can help you design a secure, scalable IoT connectivity architecture that avoids common mistakes and future risk.




.avif)